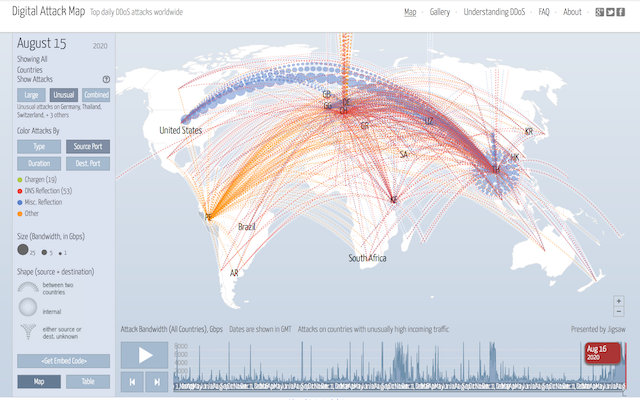
Your business is riding on the availability and integrity of your website and online services. The next Distributed Denial of Service (DDoS) attack could wreak financial havoc, compromise your customers and damage your reputation.
Unfortunately, DDoS attacks are increasing in scale, frequency and sophistication. And alarmingly, they’re easier than ever to execute. These days, anyone with an internet connection and a grievance can launch a DDoS attack for as little as $5.00.
What’s worse, everyone’s fair game. Not just the big banks, government or e-commerce sites. From FTSE 100 Companies to emerging growth companies, no organization is too insignificant to be the target of a criminal or “hacktivist” attack.